What is Hacking in Cybersecurity?: Explained
The digital landscape has transformed dramatically over the past decade, and with it, the threat of cybersecurity breaches has become increasingly sophisticated. As we move deeper into 2026, understanding what hacking is and how to defend against it has become essential for businesses and individuals alike. Cyber hacking—the unauthorized access to computer systems, networks, or data—has evolved from a niche concern to a widespread threat affecting organizations of all sizes, from multinational corporations to small startups and individual users.
This comprehensive guide explores the current state of hacking in cybersecurity, examines various attack methods, analyzes real-world incidents, and provides actionable strategies to protect yourself and your organization from cyber threats. Whether you're a business leader, IT professional, or concerned individual, understanding the mechanics of hacking is the first step toward building robust security defenses.
Understanding Hacking: Definition and Core Concepts
At its core, hacking refers to the unauthorized and deliberate exploitation of vulnerabilities within computer systems, networks, or applications to gain access to sensitive information or resources. While the term "hacking" originally referred to any unconventional approach to programming, modern cybersecurity usage specifically describes malicious activities undertaken without permission from system owners.
Cyber hacking typically serves several criminal objectives: financial theft, intellectual property acquisition, data espionage, system sabotage, or ransom extortion. However, not all hacking falls into the malicious category. Ethical hackers work legitimately with organizations to identify security weaknesses before criminals can exploit them, strengthening overall cybersecurity posture.
Key Characteristics of Hacking in 2026
Modern hacking exhibits several defining characteristics that distinguish it from earlier forms of cybercrime. Current attacks are highly targeted, often involving extensive research into victim organizations before the actual breach. Attackers frequently combine multiple techniques—a practice known as multi-vector attacks—to overcome layered security measures. Additionally, the automation of attacks through artificial intelligence and machine learning has dramatically increased the speed and scale at which hackers can identify and exploit vulnerabilities.

The Evolution of Cyber Hacking: From Past to Present
The history of hacking provides valuable context for understanding current threats. When computers first became widespread, "hackers" were primarily enthusiasts interested in pushing technological boundaries. As internet connectivity expanded and digital assets became increasingly valuable, criminal elements co-opted hacking techniques for financial gain.
The evolution has been marked by several critical phases. In the early 2000s, relatively simple worms and viruses dominated the threat landscape. The 2010s saw the emergence of sophisticated, targeted attacks against specific organizations and government entities. Today, in 2026, we're witnessing hyper-personalized attacks that leverage artificial intelligence, advanced social engineering, and zero-day vulnerabilities that remain unknown to security vendors.
Historical Context and Modern Implications
Understanding this evolution matters because modern attackers employ lessons learned from decades of cybercrime. They've developed sophisticated toolkits, established underground marketplaces for stolen data, and created organized structures resembling legitimate businesses. The sophistication level has reached the point where a single successful attack can compromise millions of user records and cost organizations billions in damages.

Common Hacking Techniques and Methods Explained
Hackers employ diverse methods to penetrate systems and networks. Understanding these techniques is essential for recognizing threats and implementing appropriate defenses.
Brute Force Attacks
Brute force attacks involve attempting countless password combinations until finding the correct credentials. While conceptually simple, these attacks can be effective against weak passwords or systems without rate-limiting protections. Automated tools dramatically increase the speed of these attacks, allowing hackers to test thousands of combinations per second.
Phishing and Social Engineering
Phishing remains one of the most effective hacking methods because it exploits human psychology rather than technical vulnerabilities. Attackers craft deceptive emails, messages, or websites that impersonate legitimate organizations, tricking users into divulging passwords, financial information, or other sensitive data.
Social engineering extends beyond phishing to include pretexting (creating false scenarios), baiting (offering something enticing), and tailgating (following authorized personnel into restricted areas). These psychological manipulation techniques are increasingly combined with technical exploits for maximum impact.
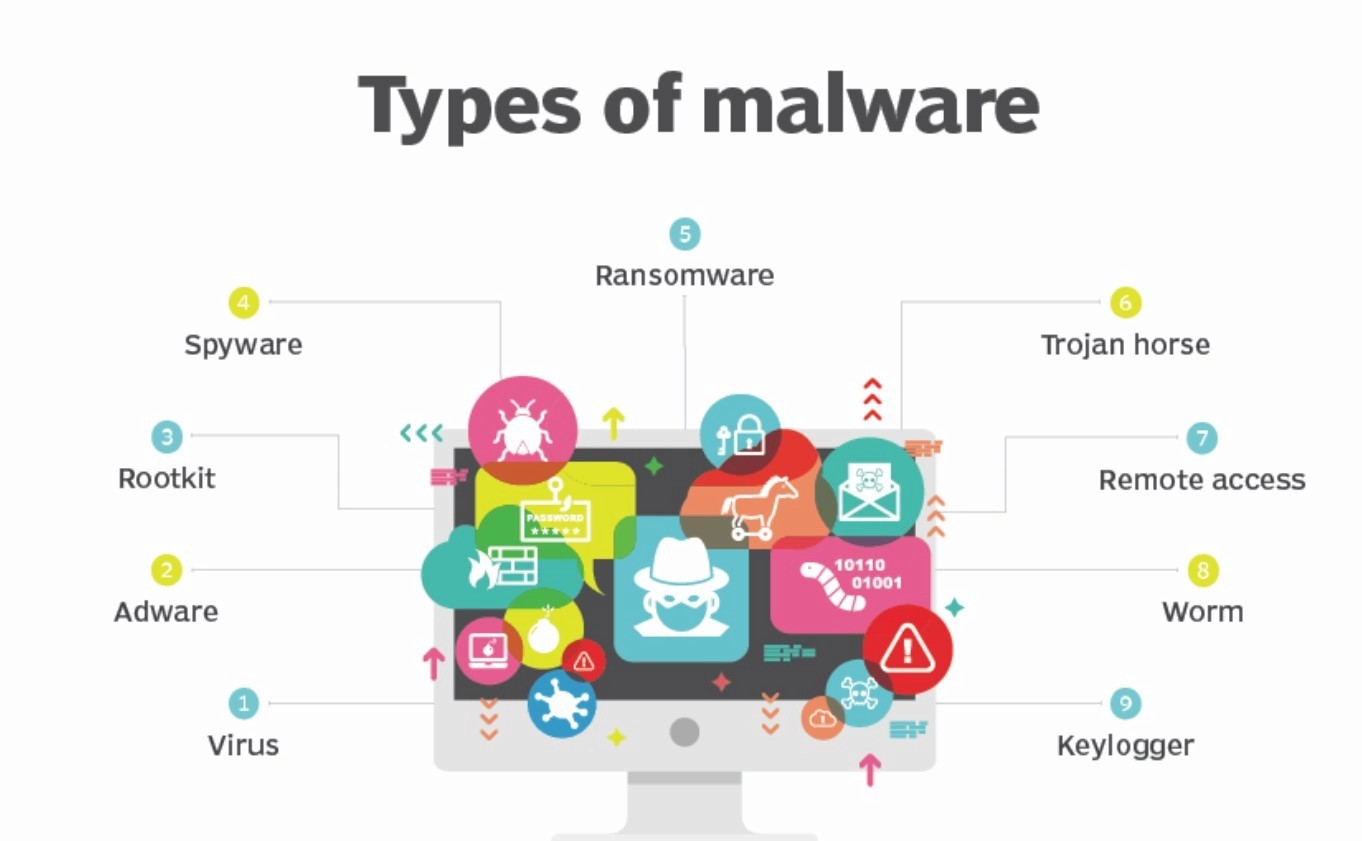
Malware and Ransomware Attacks
Malware—malicious software designed to damage or exploit systems—takes various forms: viruses that self-replicate, worms that spread across networks, trojans that disguise harmful functions, and spyware that monitors user activity.
Ransomware, a particularly devastating variant, encrypts victim data and demands payment for decryption keys. Recent ransomware campaigns have targeted critical infrastructure, healthcare systems, and large enterprises, with ransom demands frequently exceeding millions of dollars.
Zero-Day Vulnerabilities
Zero-day exploits target previously unknown security flaws for which no patch exists. Named for the "zero days" available for developers to respond before attacks begin, these vulnerabilities are exceptionally valuable in the criminal underground and represent an ongoing arms race between security researchers and malicious actors.
Distributed Denial-of-Service (DDoS) Attacks
DDoS attacks overwhelm targeted systems with traffic from multiple sources, rendering them unavailable to legitimate users. By flooding networks or servers with requests, attackers can disable websites, interrupt services, and cause significant operational disruption.
SQL Injection and Code Exploitation
SQL injection attacks exploit vulnerabilities in web applications that interact with databases. By inserting malicious code into input fields, attackers can manipulate database queries, access unauthorized information, or modify data. This technique demonstrates how even small application vulnerabilities can have catastrophic consequences.
Network Exploitation: Passive vs. Active Approaches
Network exploitation involves leveraging system tools and access methods to compromise network security. Understanding the distinction between passive and active exploitation is crucial for defenders.
Passive Network Exploitation involves reconnaissance—gathering information about target systems without directly accessing them. Attackers may monitor network traffic, analyze publicly available information, or identify system configurations. While seemingly benign, passive gathering creates the foundation for more damaging active attacks.
Active Network Exploitation directly attacks systems using tools and malicious code to gain control, access data, or disrupt services. Active attacks may involve injecting malware, exploiting known vulnerabilities, or leveraging compromised credentials. These attacks produce immediate, observable impacts on system functionality.
Security Breaches: What Happens When Defenses Fail
A security breach occurs when hackers successfully penetrate organizational defenses and access, steal, or modify sensitive information. The consequences extend far beyond immediate financial losses.
Immediate and Long-Term Impacts
Organizations experiencing breaches face multiple consequences: direct financial losses from theft, substantial costs for incident response and remediation, regulatory fines under data protection laws, erosion of customer trust, and potential business closure. The average cost of a data breach in 2026 exceeds $4 million, with impacts to brand reputation often exceeding direct financial damages.
Customers and employees affected by breaches may experience identity theft, fraudulent charges, or personal privacy violations. The psychological impact of knowing one's personal data has been compromised contributes to declining consumer confidence in organizations that fail to maintain adequate security.
Real-World Case Studies: Learning from Major Incidents
Examining significant hacking incidents provides practical insights into attack sophistication and consequences.
Yahoo Data Breach (2013-2016)
Yahoo's massive breach affected approximately 3 billion accounts, making it one of the largest data compromises in history. The breach involved unauthorized access to email addresses, passwords, phone numbers, and personal security questions. Attackers exploited SQL injection vulnerabilities and inadequate security monitoring. The incident resulted in substantial financial losses and severely damaged Yahoo's reputation and market valuation.
WannaCry Ransomware (2017)
The WannaCry ransomware attack leveraged a Microsoft Windows vulnerability (EternalBlue) to spread across 150 countries, affecting approximately 230,000 computers. Organizations paid millions in ransom to recover encrypted data. This incident demonstrated how a single unpatched vulnerability could have global consequences and highlighted the critical importance of timely software updates.
Twitter Account Takeover (2020)
A social engineering attack targeting Twitter employees resulted in unauthorized access to prominent accounts, including those of Bill Gates and Elon Musk. Attackers used these accounts to promote cryptocurrency scams, generating over $100,000 in fraudulent Bitcoin payments. The incident exposed vulnerabilities in employee security awareness and administrative access controls.

Essential Cybersecurity Measures and Best Practices
Protecting against hacking requires a comprehensive, multi-layered approach incorporating technological solutions, organizational processes, and user behavior change.
Technical Defenses
Implement firewalls to monitor and control network traffic, deploy intrusion detection systems to identify suspicious activity, and maintain antivirus software updated with current threat definitions. Use encryption for sensitive data both in transit and at rest to ensure that even if accessed, information remains unreadable without proper decryption keys.
Access Control and Authentication
Enforce strong password policies requiring minimum length, complexity, and regular updates. Implement multi-factor authentication (MFA) requiring additional verification beyond passwords—such as biometric data, security tokens, or authenticator applications. This significantly reduces unauthorized access risk even when passwords are compromised.
Regular Updates and Patch Management
Software vulnerabilities are continuously discovered and exploited. Establish a systematic process for promptly applying security patches and updates to all systems, applications, and firmware. Neglecting updates is among the most preventable causes of successful hacking.
Employee Training and Awareness
Technical defenses fail without human compliance. Regular cybersecurity training helps employees recognize phishing attempts, avoid social engineering tactics, and understand their role in organizational security. Simulated phishing exercises further reinforce learning by providing practical experience in identifying malicious communications.
Data Backup and Disaster Recovery
Maintain regular backups of critical data stored securely and separately from production systems. In the event of ransomware or data loss, reliable backups enable recovery without paying criminal demands or facing permanent data loss.
Incident Response Planning
Develop documented procedures for responding to security incidents, including identification, containment, investigation, and recovery phases. Clear incident response plans minimize damage by enabling rapid, coordinated response rather than chaotic scrambling during crises.
The Role of Emerging Technologies in Cybersecurity
Artificial intelligence and machine learning are transforming both attack and defense capabilities. These technologies enable sophisticated threat detection by analyzing patterns and identifying anomalies that might escape human attention. However, attackers also leverage AI to automate vulnerability discovery and craft personalized social engineering attacks.
Zero-trust security models—which assume no user or device can be trusted by default—represent a paradigm shift in cybersecurity architecture. Rather than assuming security once inside a network perimeter, zero-trust models verify every access request.
Creating a Comprehensive Security Strategy
Protecting your organization or personal data requires coordinated effort across multiple domains:
Assessment and Planning: Conduct thorough security assessments, identifying vulnerabilities and risks specific to your environment. Prioritize threats based on likelihood and potential impact.
Implementation: Deploy appropriate technical controls, establish security policies, and configure systems for optimal protection. This phase requires technical expertise and careful planning.
Monitoring and Detection: Continuously monitor systems for suspicious activity using security information and event management (SIEM) tools. Real-time alerts enable rapid response to potential incidents.
Training and Culture: Foster a security-conscious organizational culture where employees understand their critical role in defense. Regular training reinforces best practices and updates awareness of new threats.
Testing and Improvement: Conduct periodic penetration tests and security audits to validate defenses. Learn from real incidents and near-misses to continuously improve security posture.
Conclusion: Taking Action Against Cyber Threats
Hacking in 2026 represents a sophisticated, evolving threat that demands serious attention from individuals and organizations alike. The combination of advanced technology, determined attackers, and high-value targets ensures that cyber threats will remain prominent for the foreseeable future.
However, with understanding, preparation, and commitment to security best practices, you can significantly reduce your risk. Whether implementing technical controls, training employees, or developing incident response plans, each step toward comprehensive security strengthens your defenses.
The question is not whether hacking will target your systems, but whether you'll be prepared when it does. By staying informed about current threats, implementing robust security measures, and maintaining vigilance, you can protect your valuable data and systems in an increasingly hostile digital environment.
Begin your cybersecurity journey today by assessing your current security posture, identifying gaps, and implementing improvements. The investment in security now will pay dividends in protection, reduced incident costs, and preserved reputation for years to come.
Are you keen to become a cybersecurity expert? You don’t need to look any further than our CyberSecurity Master's Program! We will provide you with the cutting-edge learning and experience required to become one of the most sought-after professionals in this space. Our courses are specially designed, plus we have hands-on projects – both will give you all the skills necessary for success. As well as that, benefit from our network of experts who can offer career advice and mentorship.
Don’t miss out on such an incredible opportunity – sign up now for our CyberSecurity Master Program!
Happy Learning!
The founder of Network Kings, is a renowned Network Engineer with over 12 years of experience at top IT companies like TCS, Aricent, Apple, and Juniper Networks. Starting his journey through a YouTube channel in 2013, he has inspired thousands of students worldwide to build successful careers in networking and IT. His passion for teaching and simplifying complex technologies makes him one of the most admired mentors in the industry.




