In this lesson, we will discuss what is port security? And what role it plays in security? So stay tuned till the end and learn with Nwkings.
Layer 2 security is very crucial to secure the LAN networks. Switch is directly connected with end hosts. So, there is a possibility that attackers might gain the physical access of end host and infect the host with malicious content and then infect the switch.
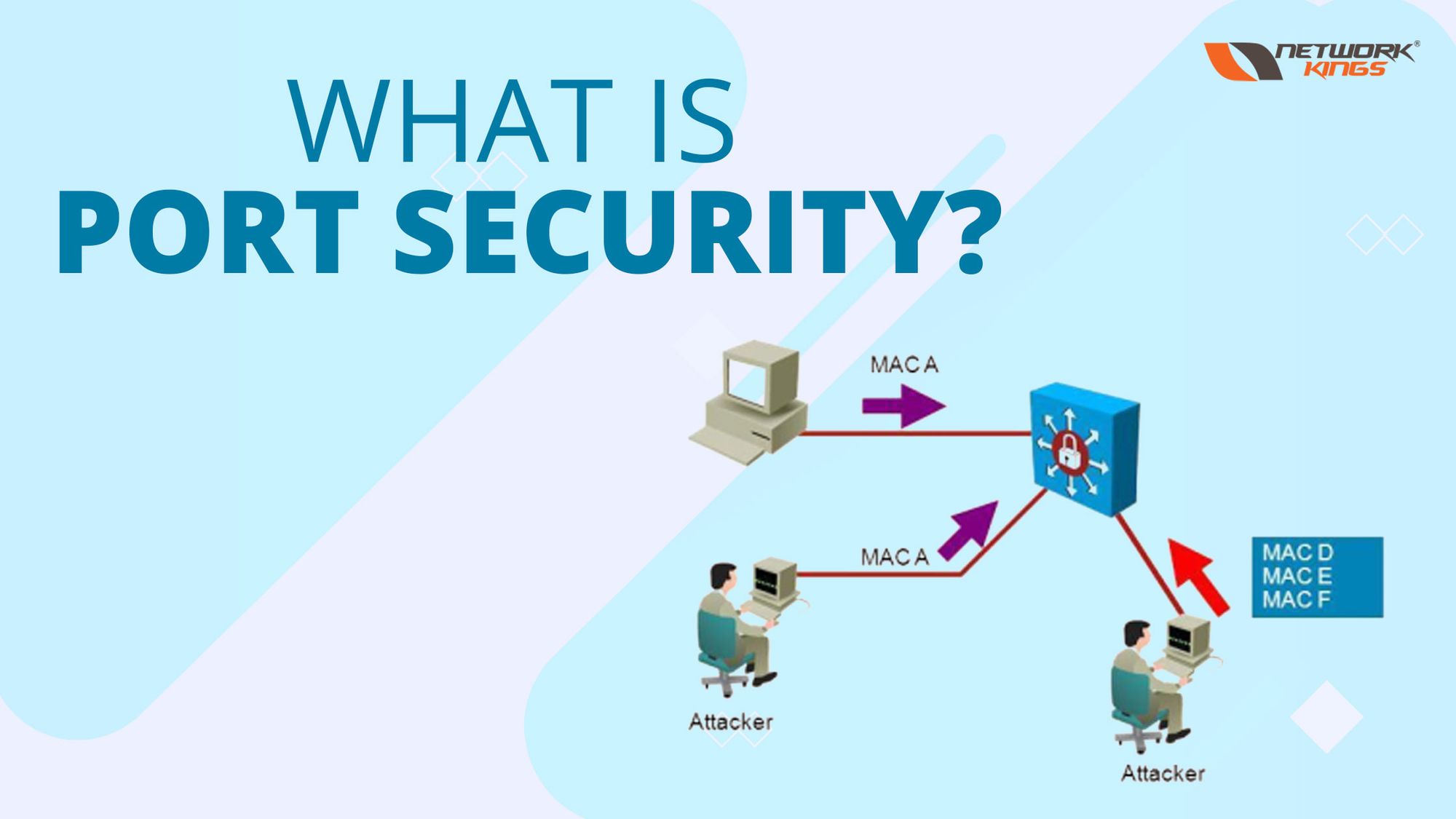
To reduce this kind of risk, port security is enable on the switch ports. So that only allowed user can access the port. Port security identifies devices based on the source MAC address of Ethernet frames. Whenever an unauthorized user (other than allowed user) tries to access the port or send the frame, it first checks the MAC address and when it found unauthorized user, the port goes into violation mode (by default violation mode is shut down).

Let’s understand with an example, in above diagram there are 2 PCs- PC1 is valid PC and PC2 is unauthorized PC. On port fa0/1 port security is enabled and PC1 is connected to this port. When PC1 send frames, it checks the MAC address as this MAC address is allowed on this port, switch will behave normally and forward the packet.
But when PC2 tries to connect with same fa0/1 port, the port doesn’t work. When PC2 will send frame, it check the MAC address, as PC2 MAC address is B.B.B that is not allowed on this port, it sends the port into violation mode.
How to configure port security?
interface <interface type> <interface name>
switchport mode access
switchport port-security
Note: To configure port security command a port should be a manually configured trunk port or access port. Dynamic auto or dynamic desirable modes are not allowed.

You can see in above image, when I first configured switchport port-security command, a message is appeared that showing command is rejected because port is dynamic port.
So, second time when I did configuration, I first configured switchport mode access command to make port access port and then configure switchport port-security command.
What is port security violation?
When a rogue host(or any host who is not allowed to access that port) tries to connect the switch port on which port security is enable, port security violation occur. In simpler words, a host who is not allowed to access that port but still tries to connect the port or sends the frame to that port, then violation occurs.
Violation mode defines how a port will behave when violation occurs. There are 3 violation modes.
- Shutdown mode
- Restricted mode
- Protect mode
By default, mode is shutdown mode.
Shutdown mode:
In this mode, port goes shut down.
Generate a syslog message when interface is disabled.
The violation counter is set to 1 when interface is disabled.
Restrict Mode:
In this mode, packet is discarded, but the port remains enable.
Generate a syslog message every time when an unauthorized MAC is detected.
Violation counter is incremented by 1.
Protect Mode:
In this mode, port discards the packet, but port remains in enable mode.
No syslog message is generated.
No violation counter.
Default settings of enable port security:

By default, violation mode is shutdown mode.
You can change this by manually configure below command-
swicthport port-security violation < violation mode name>
By default, allowed MAC address is only 1.
You can change this by manually configure below command-
Swicthport port-security maximum <number of allowed MAC address>