Access Control List
Introduction:
ACL stands for Access Control List. ACL name itself define its function, ACL rules are configured to control the access inside the network (which hosts are allowed and which aren’t). Sometime ACL also known as packet filter firewall, as ACL filters the packet based on configured rules, it decides which packet is permit and which packet is deny.
When ACLs are used to filter the packets, it performs to 2 functions depending on the rule either allow the packet or drop the packet. Packet filter simply means it filter out the packets.
ACL filter traffic based on source/destination IP addresses, source/destination layer 4 ports.
Generally, an ACL command look inside the packet header and discard the packet if any of the field is matched.
ACL rules are configured in routers or layer 3 switches.
To clear the concept of ACL, here I am giving you a general example that will give more clarity.
ACL is similar like a safety guard who sits on the gate. Let’s suppose, he has 2 list of people, one is for people who are not allowed to come in and another one for people who are not allowed to go out the society(some kids), whenever a person come in or go out, he first checks the list and then allowed the people.
In this example, safety guard is ACL, 2 different lists are two different set of ACL rules which are applied on inbound and outbound direction. Here safety guard filters the people on the basis of list similar way, ACL filters the packets on the basis of configured rules.
ACL location and direction:
The ACL must be applied to an interface. ACLs are applied either inbound (interface through which packet enters) or either outbound (interface through which packet exits). Only 1 ACL can be applied to a single interface per direction. So, in total we can apply 2 ACLs, one is inbound and another one is outbound.
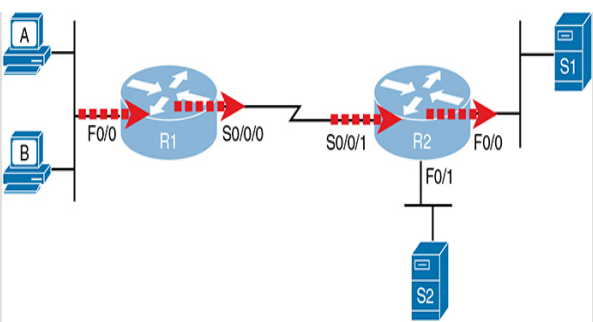
According to above diagram, to filter the traffic from host A and host B to server side, we have four locations to configure ACLs (4 right marks of arrow sign are showing interfaces location). Here 2 are inbound interfaces – Fa0/0(R1) and S0/0/1(R2) and 2 are outbound interfaces – S0/0/0(R1) and F0/0 (R2).
ACLs are made up of one or more ACEs (Access control entries) or ACL statements.
When a router checks a packet against the ACL, it process from top to bottom.
If the packet matches with ACL entries, it takes action and stops processing the ACL.
What is an implicit deny?
What will happen if a packet doesn’t match any of the entries in an ACL?
There is an implicit deny at the end of all ACLs. The implicit deny tells the router to deny all traffic that doesn’t match any of the configured entries in the ACL.
If you want to change this default behaviour, configure a permit any at the end of the ACL.
Also, you can configure a command explicitly (manually) to deny all traffic. Now many of you are thinking, by default there is implicit deny so why we need to configure explicit deny command?
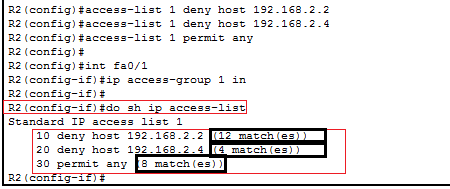
Let me explain you, ACL show commands list shows counters for the number of packets matched by each command, but there is no counter for that implicit deny. So, to see counters for how many packets are matched by the deny any logic, we configure deny any explicitly in the end of ACL.
Output of show ip access list:
What are the types of ACL?
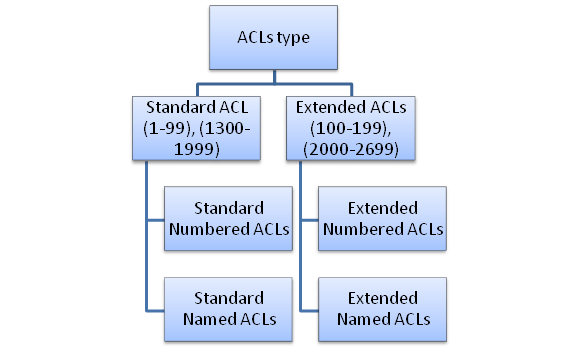
Standard ACL | Extended ACL |
1. It matches only the source IP of the packet.
2. It blocks host, subnet and a network. 3. It blocks all the services. 4. Standard ACL are simple and less accurate, only use source IP to filter the traffic. 5. Standard ACLs should be applied near to the destination. | 1. Matching parameters are layer 4 protocol/port, source IP and destination IP. 2. It blocks host, subnet and a network. 3. It blocks selected services. 4. Extended ACL are more accurate and complex as it uses more parameters to filter the traffic. 5. Extended ACLs should be applied as close to the source as possible.
|
Standard ACL:
Standard ACL are very simple, only use source IP address to match the packet.
Standard ACL use a range (1-99 and) or (1300-1999).
Standard ACL further divided into 2 types:
- Standard Named ACLs
- Standard Numbered ACLs
Note:
- Numbered ACLs are configured in global config mode.
- Named ACLs are configured with subcommands in a separate config mode.
- However, in modern IOS you can also configure numbered ACLs in the exact same way as named ACLs.
### Basic ACL Lab ###
Now we fill perform a basic ACL Lab. To perform this lab, I used packet tracer.
Objective: The objective of this lab – PC2 should access server 1, but PC1 and PC3 shouldn’t access server 1.
block 192.168.2.3 to access 192.168.1.2
block 192.168.2.4 to access 192.168.1.2
permit 192.168.2.2 to access 192.168.1.2
Before starting this lab, here are the few things that you should know.
First understand the requirements properly, according to that write the ACL statements.Before writing ACL configuration, one thing always keep in mind, ACL statements are processed top to bottom, so sequence of statements does matter.
Also, working of ACL should be clear in mind, when a packet is checked against ACL and matched with an entry, it came out and doesn’t process the remaining statements. And if a packet is not matched with any of ACL entry then default action is taken i.e. deny the packet.
Plan the location (router and interface) and direction (in or out) on that interface:
Standard ACLs should be placed near to the destination of the packets, as these are less specific and only use source IP to discard the packet.
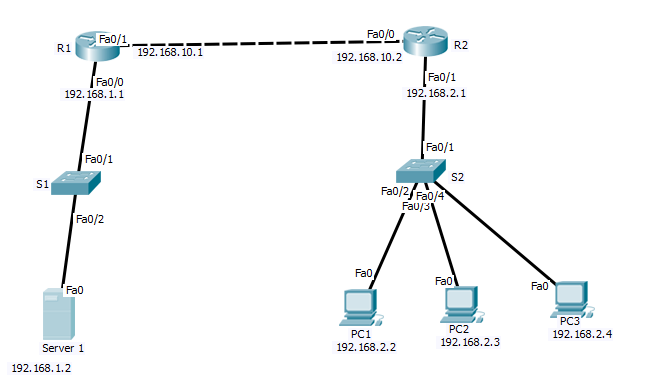
Configuration:
Configuration is looking lengthy, I agree, but it is quite simple trust me. Here I am dividing the whole configuration into parts so that you can also see how simple this configuration is?
First configure router interfaces in both routers
Configure DHCP pool to assign the IP address to hosts in both routers
Configure static routing
Configure ACL in router 2
Enable the ACL
To configure ACL, I used below commands
access-list 1 deny host 192.168.2.3
access-list 1 deny host 192.168.2.4
access-list 1 permit any
To enable ACL on interface fa0/1 of R2, I use below commands
int fa0/1
ip access-group 1 in
## R1 configuration ##
R1
enable
configure terminal
hostname R1
int fa0/1
ip address 192.168.10.1 255.255.255.0
no sh
int fa0/0
ip address 192.168.1.1 255.255.255.0
no sh
ip dhcp pool A
network 192.168.1.0 255.255.255.0
default-router 192.168.1.1
ip route 192.168.2.0 255.255.255.0 192.168.10.2
## R2 configuration##
enable
configure terminal
hostname R2
int fa0/1
ip address 192.168.2.1 255.255.255.0
no sh
int fa0/0
ip address 192.168.10.2 255.255.255.0
no sh
ip dhcp pool B
network 192.168.2.0 255.255.255.0
default-router 192.168.2.1
ip route 192.168.1.0 255.255.255.0 192.168.10.1
access-list 1 deny host 192.168.2.3
access-list 1 deny host 192.168.2.4
access-list 1 permit any
int fa0/1
ip access-group 1 in
Result: before checking result first look at your objectives. And then verify results, objective is achieved or not. According to objective, in result PC1 and PC3 should not able to ping server 1. PC1 is able to ping server 1.
Now let’s see the results

You can see in above image PC1 got ping reply in both cases. So, objective is fulfilled (permit 192.168.2.2 to access 192.168.1.2).

You can see in above result PC2 is able to ping before ACL configuration, but didn’t get ping reply after configured ACL. Objective is achieved (block 192.168.2.3 to access 192.168.1.2).

You can see in above result PC3 is able to ping before ACL configuration, but didn’t get ping reply after configured ACL. Objective is achieved (block 192.168.2.4 to access 192.168.1.2).


