
Cybersecurity means protecting systems, networks, and programs from digital attacks as they usually aim at accessing, changing, or destroying sensitive information; extorting money from users; or interrupting normal business processes. Since it has become a vital component of technology, numerous threats and attacks have been interrupting the work capacity of an enterprise. Therefore, here we bring the best ways to secure your data from hacking. So, do read the blog to learn the methods in detail.
What are the different kinds of hackers?
There are different kinds of hackers out there. Some are White Hat Hackers, some are Black Hat Hackers, and some are Grey Hat Hackers.
- White Hat Hackers
They refer to ethical hackers who break into computer systems to find and fix vulnerabilities before malicious hackers can exploit them. They use hacking skills to find vulnerabilities in websites and apps and provide solutions to fix them. There are different types of hackers, and white hat hackers are the most common. They get hired by big companies to find security loopholes to guard against malicious cyberattacks.
- Black Hat Hackers
They use their computer skills to break illegally into systems and computer programs. They usually do this for personal financial gain and are often associated with cybercrime. They break into computer networks, websites, or apps and steal information, such as credit card numbers, or cause damage to the systems. Black hat hackers also use malware to infect systems and steal information.
- Grey Hat Hackers
They are also known as ethical hackers, and they use their computer skills to break into computer systems, but they don’t break any computer programs. They aim to find vulnerabilities in websites and apps and provide solutions to fix them before malicious hackers can exploit them.
What is the purpose of hacking?
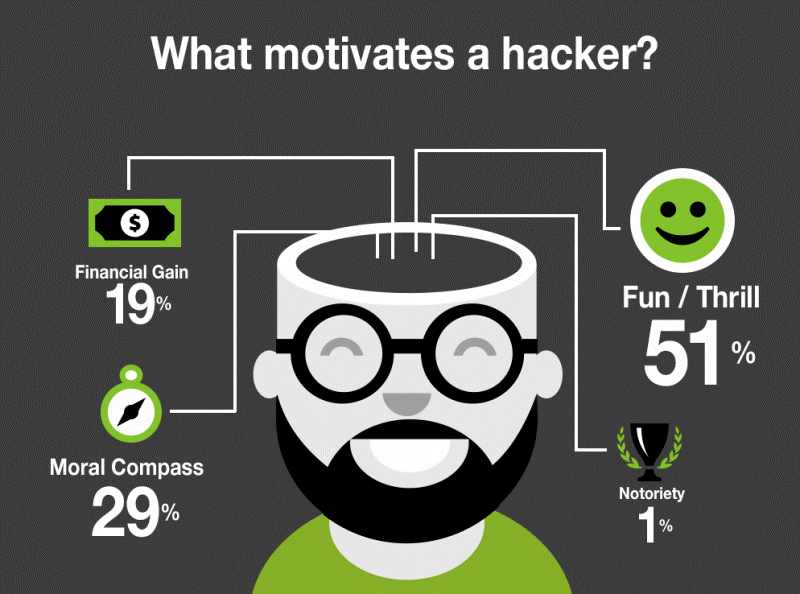
Hackers break into computers and networks for various reasons, such as stealing data, extorting money from users, and interrupting normal business processes. Computer hacking is executed by breaking into computers and networks with malicious intent. It is a serious cybercrime. Cybercriminals may hack into your computer to access sensitive information such as usernames, passwords, credit card numbers, and other private information.
Hackers may also try to take control of your computer or network, lock you out of your system, or cause damage to your files or programs. If a hacker breaks into your computer, they can access information stored on it, including your passwords, account numbers, and inlet information. If they break into a network server, they can access information stored on other computers connected to the server.
What are the different kinds of hacking?
There are many types of hacking, with various methods used to access systems and break into networks and computers.
- Network Intrusion
This kind of hacking refers to breaking into a computer network, such as a company’s internal network, to steal information or damage the network. Hackers may use malware to create a “botnet”, a network of infected computers to be controlled remotely. Once inside, they may steal information, damage computer systems, or interrupt the network’s operation.
- Data Breach
This kind of hacking refers to breaking into systems such as websites or apps and stealing information such as credit card numbers, inlet information, or personal identification information. The hackers may then try to use the stolen information to break into other systems, such as banks or airline booking systems.
- Denial of Service Attack

This kind of hacking refers to disrupting the operations of computer systems, networks, or websites by overwhelming them with network requests from many sources. The hacker may try to shut down a website or prevent users from accessing it by using various methods to flood the website with network requests from many sources. –
- Password cracking:
It provides access to computer systems or websites by guessing a user’s password. The hacker’s computer program tries to find a password that matches the one used by the user.
What are the top ways to secure your data from hacking?
There are seven excellent ways to secure your data from hacking:
- Stay updated with the latest technology updates. Keep track of the latest cyber threats and vulnerabilities.
- Use strong and unique passwords for all your online accounts, and avoid using simple words or phrases that someone can guess. Use a password manager if you want to store your passwords electronically.
- Keep your antivirus or internet security software up-to-date. Install any software updates and patches issued by the software developer.
- Be careful while clicking on links or downloading files from the internet. Avoid downloading any software or clicking on any link that looks suspicious.
- Don’t share your personal information publicly. Avoid using your full name, birthday, or other personal information in your account names or as your password.
- Don’t click on any link that asks for your password or other personal information, such as a phone call or email. If you receive an email from your bank or any other financial institution asking for your login information, contact them directly using the phone number on the website.
- Don’t click on links from people you don’t know; if you get an email or text message from someone you don’t know, don’t respond to it and don’t open any attachments or links it might contain.
Wrapping Up!
Cybersecurity is a complex challenge that requires constant attention and investment. It is necessary to understand the threats and vulnerabilities and implement defensive measures to protect your data and systems. While there is no 100% secure system, there are many ways to improve your cybersecurity to minimize the risk of a cyberattack. Hence the blog Seven Ultimate Ways To Secure Your Data From Hacking will help you to surf securely online!


