Network Firewall Interview Questions and Answers for 2026 Jobs
Whether you’re appearing in an interview to become a Network Security Engineer, Firewall Engineer, or even a Cybersecurity Engineer; it is very important to be aware of basic network firewall security.
If you’re appearing for any of the above interviews, then you’re at the right place. This blog will also help those who want to learn more about firewalls and network security in general. Hold tight, we are about to begin with the most-asked Network Firewall interview questions.
These Firewall interview questions are the most frequently asked in the industry. Let’s begin!
Basic Firewall Interview Questions and Answers
1. What is a firewall?
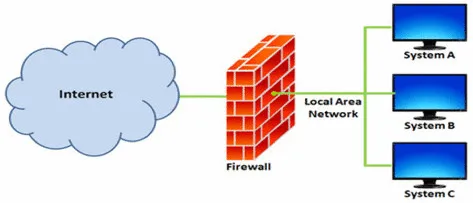
A firewall acts as a line of defense in a network. It acts as a barrier between a trusted and a non-trusted network.
It allows/blocks incoming or outgoing traffic on the basis of pre-configured policies or rules.
Firewalls are the oldest and most frequently used network security solutions.
A firewall could be a free or a paid software solution.
A firewall also works to protect internal networks from each other.
2. What is a packet-filtering firewall?
A packet filtering firewall examines the source and destination IP addresses, protocols such as User Datagram Protocol (UDP) and Transmission Control Protocol (TCP), as well as port addresses.
The packet is verified and secured if both IP addresses match each other.
3. What is the difference between stateful and stateless firewalls?
Based on their state, the packet filtering firewalls can be classified into two types:
Stateful packet filtering firewalls
Stateless packet filtering firewalls
Stateful packet filtering firewalls:
A stateful firewall is located in Layer 3 and Layer 4 of the Open Systems Interconnection (OSI) model.
It keeps track of the state of network connections.
This means that it knows the current status of the process.
This firewall adds the traffic to a stable table once it is approved.
Stateful firewalls are able to detect fake messaging and unauthorized access.
They have a powerful memory as they remember the main aspects of network connections.
They have stronger attack mitigation.

Stateless packet filtering firewalls:
Stateless firewalls are also known as Access Control Lists (ACLs).
They are not aware of the current state of connection/incoming traffic.
ACLs are present in the network or physical layers and sometimes, in the transport layer.
The device accepts or rejects an incoming packet by checking if it matches the ACL rules or not.
Stateless firewalls are faster than stateful firewalls.
They perform better in heavy traffic as they do not dive deep into the information of a packet, as stateful firewalls do.

4. What is the function of a firewall?
The function of a firewall is to protect sensitive enterprise systems, be it any basic firewall or an advanced Next Generation (NGFW) firewall as a FortiGate firewall.
A firewall is able to recognize harmful or malicious traffic.
It is able to block traffic from a particular IP address if it senses any malicious activity in them.
It acts as a filtering unit for legal and healthy traffic.
An advanced firewall can also look into the contents of data packets and look for malware signatures.
5. How does a firewall function?
A firewall filters traffic on the basis of a set of configurations or rules that are applied by a firewall administrator. It has the ability to permit or block any IP address, port number, web application, and network-layer protocols on the basis of these rules.
Some of the common ports are as follows:
80 HTTP
25 SMTP
22 SSH
23 Telnet
443 HTTPS
20 and 21 FTP
6. Can IPSec ever rule out firewalls?
The function of an IPSec is to provide host-to-host authentication and encryption. It is a group of protocols used together to set up encrypted connections between network devices.
Firewalls, on the other hand, protect the network without encryption or host-to-host authentication. It filters the traffic and permits/blocks based on a certain set of rules.
This means that both IPSec and firewalls are needed because of their specific functions. IPSec cannot cause the expiration of firewalls. Although we can consider IPSec-enabled hosts in the future.
7. What do you understand by a VPN?
The full form of a VPN is Virtual Private Network (VPN).
It creates a safe and secure connection between the Internet and your device.
Once you are connected to the internet through a VPN, your data is sent via an encrypted virtual tunnel.
It also creates a connection between two private networks over the internet.

The detail page will display content pulled from the first entry of the collection by default. In order to preview other items in the collection, change the content by selecting a different item from the dropdown menu.
8. What are the different types of firewalls in network security?
There are five types of firewalls in network security. These are as follows:
Packet filtering firewalls
Application-level gateway or Proxy firewalls
Circuit-level gateway firewalls
Stateful inspection firewalls
Next-Generation firewalls (NGFW)
9. Firewalls work in which OSI layers?
A firewall works at these three layers in the OSI model, namely:
Layer 3 (Network layer)
Layer 4 (Transport layer)
Layer 7 (Application layer)
10. What is the function of a transparent firewall?
A firewall acts as a Layer 2 device, like a bridge or switch, in transparent mode.
It then forwards Ethernet frames on the basis ofthe destination MAC address.
The best part about a transparent firewall is that it can be easily inserted in an already existing segment to control the traffic between two sides without readdressing or reconfiguring the devices.
11. What is Policy NAT?
Policy NAT stands for Policy Network Address Translation.
It allows you to NAT by giving both the source and destination addresses in an extended Access List (ACL).
We can also give source and destination ports.
There are two types of Policy NAT available:
Static Policy NAT
Dynamic Policy NAT
12. What is the default timeout value for TCP, UDP, and ICMP sessions?
The default value for a TCP session is 60 minutes.
The default value for the UDP session is 2 minutes.
The default value for the ICMP session is 2 seconds.
FAQs:
01. What is a firewall in Networking?
A firewall acts as a line of defense in a network. It acts as a barrier between a trusted and a non-trusted network. It allows/blocks incoming or outgoing traffic on the basis of pre-configured policies or rules.
02. What are the types of firewalls?
Packet filtering firewalls, Application-level gateway or Proxy firewalls, Circuit-level gateway firewalls, Stateful inspection firewalls, Next-Generation firewalls (NGFW)
03. Give some examples of firewalls.?
The most popular firewalls in the market are the Palo Alto firewall, Checkpoint firewall, FortiGate firewall, etc.
04. How does a firewall function?
A firewall filters traffic on the basis of a set of configurations or rules that are applied by a firewall administrator.
05. What are the three types of firewall delivery methods?
Hardware-based firewalls, Software-based firewalls, Cloud/hosted firewalls
06. Is the firewall Layer 3 or Layer 4?
A firewall works in both Layer 3 and Layer 4. In fact, in the advanced OSI model, the firewalls work in Layer 7 as well.
07. Is VPN a Layer 4?
A VPN usually sits at Layer 3, the Network layer.
08. Does the firewall have a router?
Yes, a lot of routers have built-in routers. It is the core of a wireless network.
The founder of Network Kings, is a renowned Network Engineer with over 12 years of experience at top IT companies like TCS, Aricent, Apple, and Juniper Networks. Starting his journey through a YouTube channel in 2013, he has inspired thousands of students worldwide to build successful careers in networking and IT. His passion for teaching and simplifying complex technologies makes him one of the most admired mentors in the industry.




