What are the Firewall Functions: Explained
In today's digital landscape, cybersecurity threats are more sophisticated and frequent than ever. Organizations face constant challenges from malicious actors seeking to breach their networks, steal sensitive data, and disrupt operations. At the foundation of every robust cybersecurity strategy sits a critical tool: the firewall.
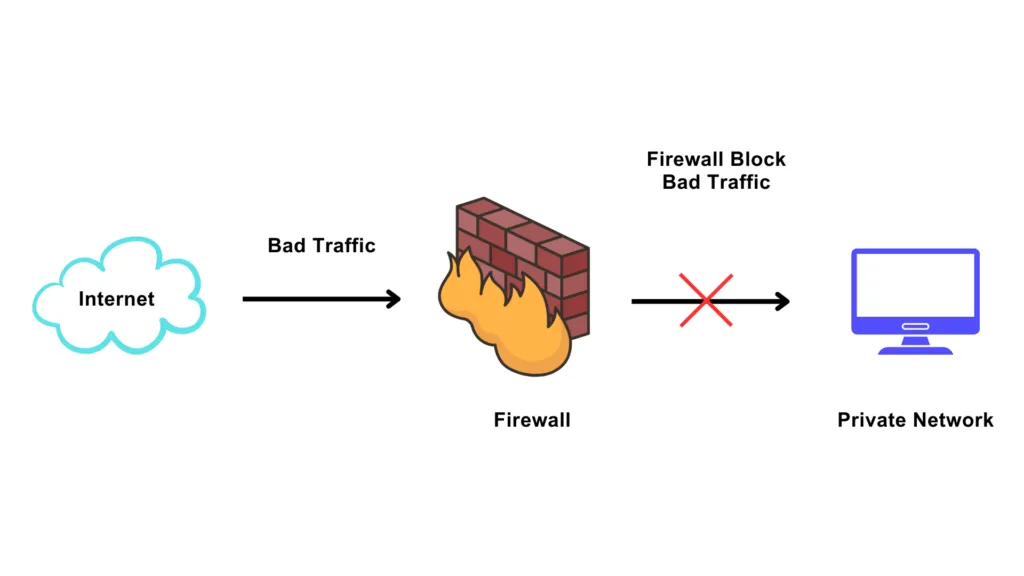
A firewall is a network security device or software application designed to monitor and control incoming and outgoing network traffic based on predefined security policies. Think of it as a digital gatekeeper—a protective barrier between your trusted internal network and the untrusted external world, particularly the internet. By establishing clear boundaries between what's allowed and what's blocked, firewalls form the first line of defense against unauthorized access and cyber threats.
Whether you're managing a small business network or securing an enterprise infrastructure, understanding how firewalls function and what they protect against is essential for maintaining network integrity and data security.

How Firewalls Work: The Fundamentals
Firewalls operate by creating distinct security zones, each with varying levels of trust and access permissions. The primary zones include:
Trusted Zone (Internal Network): This is your organization's internal network containing computers, servers, and resources you control and trust.
Untrusted Zone (External Network): This represents the internet and external networks beyond your control, where threats typically originate.
Demilitarized Zone (DMZ): A less-trusted intermediate zone that hosts public-facing services, providing an additional layer of separation between the internet and critical internal systems.
The fundamental principle governing firewall traffic flow is asymmetrical: traffic from the trusted zone to the untrusted zone is generally allowed, while traffic attempting to enter from untrusted zones is blocked by default. Each zone is assigned a security value, and traffic from lower-security zones cannot reach higher-security zones without explicit permission.
Administrators have full flexibility to customize these rules and manipulate traffic flow according to their organization's specific security needs and business requirements.

What are the key functions of a firewall?
1. Network Security and Threat Prevention
The most critical function of a firewall is to provide robust network security. Firewalls act as vigilant sentries, continuously monitoring network traffic in real-time to identify and block threats before they can penetrate your system.
They examine incoming data packets and compare them against established security rules. Suspicious traffic patterns, known malicious IP addresses, and attempted intrusions are identified and blocked immediately. By filtering potentially harmful or suspicious data packets, firewalls significantly reduce your exposure to cyber threats originating from untrusted networks.
2. Access Control and Permission Management
Firewalls empower administrators to implement sophisticated access control policies that dictate precisely who and what can access the network. These granular controls allow you to:
Define rules based on source and destination IP addresses
Control access by port numbers and protocols
Restrict specific applications or services
Create user-based access policies
Set time-dependent access restrictions
This level of control ensures that only authorized users and legitimate traffic reach your network resources, while unauthorized access attempts are systematically denied.
3. Protection of Sensitive Data
Data protection is a paramount concern for modern organizations. Firewalls safeguard sensitive and confidential information—including proprietary business data, personal customer information, and financial records—by preventing unauthorized access and data exfiltration.
By controlling which external entities can access your internal resources, firewalls maintain data confidentiality and integrity. They create a protective perimeter that makes it significantly more difficult for attackers to reach and compromise valuable data assets.
4. Prevention of Malware and Cyber Attacks
Firewalls provide active defense against sophisticated threats, including:
Malware and viruses: Blocking infected files and known malicious signatures
Worms and ransomware: Preventing self-propagating threats and encryption-based attacks
DDoS attacks: Filtering malicious traffic floods designed to overwhelm systems
Intrusion attempts: Blocking unauthorized connection attempts from known threat sources
By identifying and blocking malicious traffic patterns before they reach your network, firewalls prevent entire categories of cyber threats from establishing footholds in your systems.
5. Network Segmentation and Isolation
Firewalls facilitate strategic network segmentation by dividing your network into separate zones, each with customized security policies. This architectural approach provides multiple critical benefits:
Threat containment: If one segment is compromised, the damage is isolated and cannot spread throughout the entire network
Reduced attack surface: Segmentation limits the areas attackers can access, even if they breach the perimeter
Improved performance: Network traffic can be optimized by directing data through appropriate channels
Compliance support: Segmentation helps meet regulatory requirements by isolating sensitive data
6. Compliance with Regulatory Requirements
Many industries operate under strict security and compliance regulations that mandate firewall implementation as a foundational security measure. These standards include:
HIPAA for healthcare organizations
PCI DSS for payment card processing
GDPR for organizations handling EU resident data
SOC 2 for service providers
ISO 27001 for information security management
Implementing and properly configuring firewalls demonstrates your organization's commitment to security best practices and helps you meet mandatory compliance audits and certifications.
7. Endpoint Protection and Device-Level Security
While network-level firewalls protect the entire network perimeter, endpoint firewalls provide an additional security layer on individual devices such as laptops, desktops, and servers. These personal firewalls:
Monitor traffic specific to each device
Prevent unauthorized access targeting individual endpoints
Protect against attacks exploiting local network connections
Provide defense even when devices operate outside the main network
This multi-layered approach ensures comprehensive security across your entire IT infrastructure.
What are the types of firewalls?
Packet Filtering Firewalls
Operating at Layer 3 (Network Layer) of the OSI model, packet filtering firewalls examine incoming packets and compare their header information—including source IP, destination IP, port numbers, and protocol type—against predefined rules.
Key Characteristics:
Stateless operation (evaluates each packet independently)
Fast performance due to minimal processing overhead
Cost-effective implementation
Requires careful rule ordering for optimal effectiveness
For example: –
Rule 1:- Allow Destination Address 172.16.1.5
Rule 2:- Deny Destination Address 172.16.1.5
Important Note: Since the rule list is viewed from top to bottom, the packet with destination address 172.16.1.5 will be allowed even though you have denied it in rule 2.
Stateful Inspection Firewalls
These advanced firewalls operate at Layers 3 and 4 (Network and Transport layers) of the OSI model. Unlike packet-filtering firewalls, they maintain a state table that tracks active connections and their contexts.
Key Characteristics:
Maintains connection state information
Evaluates packets within the context of established connections
Verifies that incoming packets belong to authorized sessions
Provides enhanced security with minimal performance impact
Represents the standard for most modern networks
When a packet matches predefined rules and is permitted, the firewall adds an entry to its state table containing source IP, destination IP, port numbers, and connection state. Subsequent packets are compared against both the rules and this state table, ensuring they're part of legitimate, authorized communications.
Proxy Firewalls
Operating at Layer 7 (Application Layer), proxy firewalls act as intermediaries between clients and servers, handling requests on behalf of users. They perform deep packet inspection, examining not just packet headers but actual data content.
Key Characteristics:
Deepest level of inspection capability
Application-aware filtering based on content
Enhanced security for web-based threats
May introduce additional latency due to processing overhead
Ideal for organizations prioritizing security over raw speed
Next-Generation Firewalls (NGFW)
NGFW solutions represent the evolution of firewall technology, integrating traditional firewall capabilities with advanced security features, including:
Intrusion Prevention Systems (IPS)
Application awareness and control
Deep packet inspection
SSL/TLS inspection
User and application-level controls
Integrated threat intelligence
Sandboxing for unknown threats
These comprehensive solutions provide defense against the sophisticated, multi-vector attacks prevalent in today's threat landscape.
Firewalls remain indispensable components of any serious cybersecurity strategy. By monitoring network traffic, controlling access, preventing malware, and enabling network segmentation, firewalls protect your organization's most valuable assets—data, operations, and reputation.
The key to maximizing firewall effectiveness lies in proper configuration, regular rule review, and selecting the firewall type that matches your organization's specific security requirements and risk profile. Whether you implement traditional stateful inspection firewalls or modern next-generation solutions, a well-designed firewall strategy forms the cornerstone of robust network security.
Investing in firewall technology and expertise today significantly reduces your organization's exposure to cyber threats and demonstrates your commitment to protecting stakeholder data and maintaining business continuity.
The founder of Network Kings, is a renowned Network Engineer with over 12 years of experience at top IT companies like TCS, Aricent, Apple, and Juniper Networks. Starting his journey through a YouTube channel in 2013, he has inspired thousands of students worldwide to build successful careers in networking and IT. His passion for teaching and simplifying complex technologies makes him one of the most admired mentors in the industry.




