Mastering VLAN Trunking with 802.1Q in Enterprise Networks for CCNA
If you're preparing for your CCNA certification, there's one topic that separates the candidates who truly understand networking from those who've simply memorized answers VLAN trunking with 802.1Q. It's not just an exam concept — it's the backbone of how modern enterprise networks segment traffic, enforce security, and scale efficiently across dozens or hundreds of switches.
This guide breaks down everything you need to know about 802.1Q trunking — from what it is and why it matters, to how it's configured, troubleshot, and applied in real enterprise environments.
What Is a VLAN and Why Does Trunking Exist?
Before diving into trunking, let's establish the foundation. A Virtual Local Area Network (VLAN) is a logical grouping of devices on a network, regardless of their physical location. VLANs allow network engineers to:
Segment traffic between departments (e.g., HR, Finance, IT)
Reduce broadcast domains and improve network performance
Enforce security policies between groups of users
Simplify network management across large environments
The challenge arises when multiple VLANs need to communicate across multiple switches. You could dedicate one physical cable per VLAN between switches — but that's inefficient, expensive, and doesn't scale. That's exactly the problem VLAN trunking solves.
A trunk link is a single physical connection between two switches (or a switch and a router) that carries traffic from multiple VLANs simultaneously. Instead of running separate cables, one trunk port handles them all.
What Is 802.1Q? The Industry Standard for Trunking
IEEE 802.1Q is the industry-standard protocol that defines how VLAN information is carried across trunk links. Before 802.1Q became widely adopted, Cisco used its own proprietary trunking protocol, ISL (Inter-Switch Link). Today, ISL is obsolete — 802.1Q is the standard you need to know for the CCNA and for real-world networking.
How 802.1Q Tagging Works
When a frame leaves an access port and enters a trunk link, the switch inserts a 4-byte 802.1Q tag into the Ethernet frame header. This tag contains:
TPID (Tag Protocol Identifier): A 16-bit field always set to 0x8100 — this signals that the frame is 802.1Q tagged
PCP (Priority Code Point): 3 bits used for Quality of Service (QoS) prioritization
DEI (Drop Eligible Indicator): 1 bit that marks frames eligible for dropping under congestion
VID (VLAN Identifier): 12 bits that identify which VLAN the frame belongs to — supporting up to 4,094 unique VLANs
When the frame reaches the destination switch, the tag is read, the frame is forwarded to the correct VLAN, and the tag is stripped before delivery to the end device. End devices never see the tag — it's entirely a switch-level operation.
The Native VLAN — A Critical Concept (and Common Exam Trap)
One of the most important — and most misunderstood — concepts in 802.1Q trunking is the Native VLAN.
On an 802.1Q trunk, frames belonging to the Native VLAN are sent untagged. By default, this is VLAN 1 on Cisco switches. Here's why this matters:
Both ends of a trunk link must agree on the Native VLAN — a mismatch causes a native VLAN mismatch error and can lead to traffic leaking between VLANs
Leaving the Native VLAN as VLAN 1 is a security risk — it's a well-known attack vector called a VLAN hopping attack
Best practice: Change the Native VLAN to an unused VLAN (e.g., VLAN 999) on all trunk links
This is exactly the kind of real-world nuance the CCNA exam tests — and the kind of thing that protects enterprise networks from misconfigurations and attacks.
Configuring 802.1Q Trunking on Cisco Switches
Here's how to configure a trunk port on a Cisco IOS switch — the commands you'll use in labs, simulations, and production environments:
Switch(config)# interface gigabitEthernet 0/1
Switch(config-if)# switchport mode trunk
Switch(config-if)# switchport trunk encapsulation dot1q
Switch(config-if)# switchport trunk native vlan 999
Switch(config-if)# switchport trunk allowed vlan 10,20,30
Breaking it down:
switchport mode trunk— Forces the port into trunking modeswitchport trunk encapsulation dot1q— Specifies 802.1Q as the encapsulation method (required on older switches)switchport trunk native vlan 999— Changes the native VLAN from the default VLAN 1switchport trunk allowed vlan 10,20,30— Restricts which VLANs are permitted on this trunk (security best practice)
To verify your configuration:
Switch# show interfaces trunk
Switch# show interfaces gigabit Ethernet 0/1 switchport
These two commands are your go-to verification tools — on the exam and in the field.
Dynamic Trunking Protocol (DTP) — Know It, Then Disable It
Cisco switches support Dynamic Trunking Protocol (DTP), which automatically negotiates trunking between connected switches. While convenient in a lab, DTP is a security liability in enterprise environments.
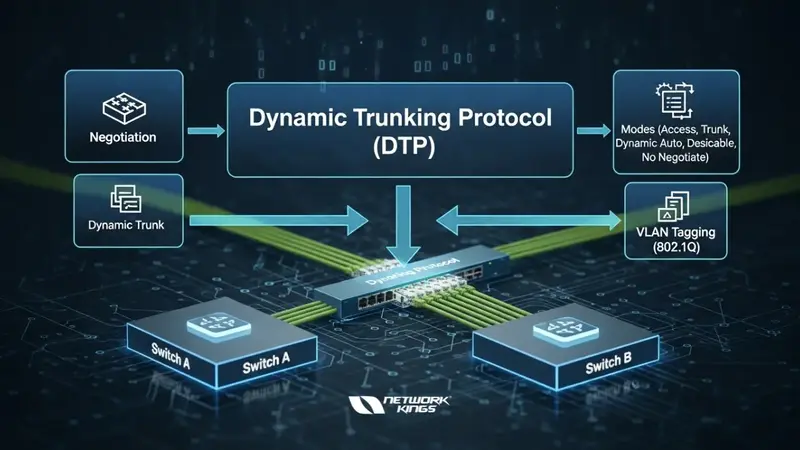
DTP modes to understand for CCNA:
Mode | Behavior |
| Passively waits to form a trunk — will trunk if the other side initiates |
| Actively tries to form a trunk |
| Forces trunking regardless of the other side |
| Forces the port to be an access port — no trunking |
Best practice: Always disable DTP on production trunk ports with:
Switch(config-if)# switchport nonegotiate
This prevents unauthorized switches from negotiating trunk links — a key security hardening step in enterprise deployments.
VLAN Trunking in Real Enterprise Environments
In a real enterprise network, 802.1Q trunking is everywhere:
Distribution-to-access layer links carry multiple VLANs to floor switches serving different departments
Router-on-a-Stick configurations use a single trunk link between a router and a switch to route inter-VLAN traffic using subinterfaces
Server connections to VMware ESXi or Hyper-V hypervisors are trunked to pass multiple VLANs to virtual machines
Wireless access points receive trunk links to support multiple SSIDs mapped to different VLANs
Understanding trunking isn't just about passing the CCNA training and certification — it's about understanding the plumbing behind every segmented network you'll ever work on.
Common Trunking Mistakes to Avoid
Even experienced engineers make these errors — being aware of them sets you apart:
Native VLAN mismatch between trunk endpoints — causes CDP warnings and unexpected traffic behavior
Forgetting to allow VLANs on the trunk — traffic silently drops if a VLAN isn't in the allowed list
Leaving DTP enabled creates a security vulnerability in production
Not verifying with
showcommands — always confirm your config, never assume it worked.
Mastering 802.1Q VLAN trunking is one of the most rewarding milestones in your CCNA journey — because it's one of those topics where exam knowledge and real-world application are perfectly aligned. Every enterprise network you'll encounter uses trunk links. Every multi-VLAN environment depends on 802.1Q.
Understand the tagging mechanism. Nail the configuration commands. Respect the Native VLAN. Disable DTP. Verify everything.
Do those four things consistently, and you won't just pass the CCNA — you'll be ready to configure and troubleshoot enterprise networks from day one on the job.
The founder of Network Kings, is a renowned Network Engineer with over 12 years of experience at top IT companies like TCS, Aricent, Apple, and Juniper Networks. Starting his journey through a YouTube channel in 2013, he has inspired thousands of students worldwide to build successful careers in networking and IT. His passion for teaching and simplifying complex technologies makes him one of the most admired mentors in the industry.




