Cisco Virtual Switching: Explained
The Cisco Virtual switching system is the technology introduced in CISCO catalyst 6500 series switches, which overcomes the drawback of EtherChannel and Spanning Tree protocol. It allows two catalyst switches to work as a single virtual switch.
Before understanding how it works and its benefits, let us first understand the Cisco Three-Layer Hierarchical Model.
What is the Cisco Three-layer Hierarchical Model?
The Cisco Three-Layer Hierarchical Model divides a network into three different layers, namely: –
The Access Layer
The Distribution Layer
The Core Layer
But why do we need these layers?
Initially, the topology of networks was called the flat topology, which looks like this: –

If we need to expand this network, more switches need to be added since the number of end devices increases. This topology restricted us to control the broadcast and undesirable traffic. With the increase in the number of devices, response time decreases, and hence the efficiency of the network reduces.
NOTE: Flat topology might work for small networks, but in the case of medium-sized and large networks, this topology is inefficient.
With the help of the Hierarchical Model, which divides the network into discrete layers, the network designer can optimize the network. Basically, with the help of this model, we divide a large network into smaller and manageable network segments. Also, the network is divided and managed in such a way that traffic that is required goes to the upper layer of the Hierarchy.

NOTE: With the help of this, the broadcast domain also increases.
Let us discuss each layer of this model: –
Access Layer
At the bottom of the hierarchy, the Access layer connects end-user devices, such as computers, printers, phones, and IoT devices, to the network. This layer ensures that devices can communicate with one another and access network resources. It provides connectivity between workstation servers.
The access layer helps to perform layer-2 switching, port security, QoS classification, Address Resolution protocol inspection, etc.
Distribution Layer
The middle layer is called the Distribution layer, which acts as a traffic aggregator and controls the data flow between the Access and Core layers. The distribution layer is responsible for managing VLANs, which helps to segment the traffic. The distribution layer helps aggregate the WAN and LAN links, provides policy-based security using ACL and redundancy, controls the broadcast domain, ensures optimal traffic distribution, and helps in routing and filtering services.
Core Layer
The Core layer is the topmost layer of the hierarchy and is responsible for high-speed, low-latency data forwarding. It connects distribution layer devices, providing a high-speed backbone that ensures rapid data transmission. The Core layer is designed for reliability, often utilizing redundancy and fault-tolerant configurations to maintain uninterrupted connectivity. It consists of high-speed Cisco catalyst devices.
What are the benefits of the Cisco Three-layer Hierarchical Model?
The benefits of the Cisco Three-Layer Hierarchical Model are as follows-
Scalability
One of the most significant advantages of the Three-Layer Hierarchical Model is its scalability. By dividing the network into distinct layers, it becomes easier to expand and adapt as your organization grows. Adding more Access layer switches or upgrading the Core layer can be done with minimal disruption to the existing network.
Management
The modular structure of the model simplifies network management. Each layer has a specific role and set of responsibilities, making it easier to troubleshoot issues. This simplicity also helps in the efficient allocation of resources and reduces the complexity of configuration.
Security
The Distribution layer’s role in traffic filtering and VLAN management enhances network security. By segmenting the network into VLANs you can isolate sensitive data and restrict unauthorized access. Additionally, the Distribution layer can implement access control lists (ACLs) to control traffic flow and protect against security threats.
Improved Performance
The Core layer’s high-speed backbone ensures rapid data transmission between different parts of the network, leading to improved performance and reduced latency, crucial for applications that demand real-time data transfer.
What is a Cisco Virtual Switching System?
We needed redundancy in the network; hence redundant links were added. Then came the problem of loops. To avoid that, the Spanning Tree protocol came into the picture. Spanning tree is a useful protocol, but it comes up with some cost. Response time decreases, and we cannot use both links at the same time for forwarding traffic since STP will block one link.
Yes, we are getting redundancy, but one of the links is useless, and we cannot do the load balancing. Sounds like an inefficient use of resources. In a Three-Layer Hierarchical Model, switches are given redundant links, but if one of the links gets blocked then it results in the wastage of resources.

VSS allows two (not more than two) separate physical switches to form a single virtual switch. It is supported by higher-end Cisco Switch series such as 45–/6500/6800.
Switches in the stack are connected via a link called Virtual Switch Link. A single link can also be used to connect two switches, but two or more links are recommended to provide redundancy. A maximum of eight links can be connected to form a single VSL.
We can even connect two switches kilometers apart and make it a VSL using fiber optic cabling.


In the case of VSS, there is a single control plane but dual active forwarding planes. VSS helps to increase the forwarding capacity along with eliminating STP loops. One of the switches attains the Active mode while the other is in standby mode.
NOTE: A switch with greater priority becomes an active switch while one with less priority becomes a standby switch.
What is a Router MAC Address?
The Router MAC address gets derived from the chassis MAC EEPROM. Since both switches now act as a single virtual switch, the MAC Address should also be single. MAC Address gets negotiated at system initialization. The MAC Address of the active switch becomes the MAC Address of the virtual switch. MAC Address remains the same even if the active switch is shut for some reason so that the host does not need to do the ARP process for a new address.
The links which connect the two switches are called Virtual Switch links. VSL passes two types of traffic: –
VSS control traffic
This traffic is used to control and maintain the Virtual Switch links.
Data Traffic
When traffic is received on one member must be sent out of an interface on the other member.
Before the Virtual Switching System is activated, the Virtual Switch link, which links the switches must be up and running. When a switch boots the configuration for VSL gets parsed first. VSL interfaces are then enabled. VSS uses a Virtual switch link protocol, which is used to establish and maintain the VSL and VSS.
What are the component protocols of the Virtual Switching System?
The Virtual Switching System has two component protocols:-
LMP
Link management protocol runs on each link that is a part of VSL and performs the following function: –
Verify link integrity by establishing bidirectional traffic forwarding.
Exchanges switch IDs and keepalive timers, hello timers, and hold timers.
RRP
Role resolution protocol performs the following function: –
Determine if the hardware and software versions of the switches are compatible or not
Determine the active and standby switches.
Depending upon the compatibility, the standby switch comes up in one of two modes: –
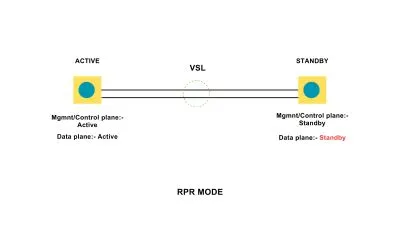
Route processor redundancy mode:- In this mode, the standby switch cannot forward traffic but is available as a backup if the active fails
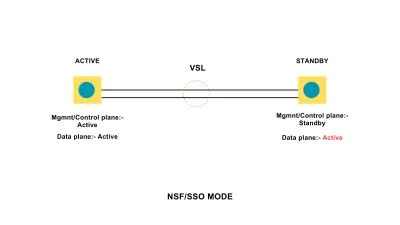
NSF/SSO:- Nonstop forwarding/stateful switchover mode, Standby switch is fully initialized and can forward traffic
Hence Virtual Switching System mainly provides two functions: –
It extends the control plan and enables synchronization of protocol and table
Data forwarding when required.
The founder of Network Kings, is a renowned Network Engineer with over 12 years of experience at top IT companies like TCS, Aricent, Apple, and Juniper Networks. Starting his journey through a YouTube channel in 2013, he has inspired thousands of students worldwide to build successful careers in networking and IT. His passion for teaching and simplifying complex technologies makes him one of the most admired mentors in the industry.




