12 Most Important Topics in CCNA Certification Course
In this article, I am going to share the 12 most important topics in the Online CCNA certification course. These are also important from an interview point of view.
1. Address Resolution Protocol (ARP):
ARP is a layer of 2 protocols. Its full form, Address Resolution Protocol, itself defines its function. A PC sends an ARP request to know the MAC address of a device. ARP request is broadcast. In response to an ARP request, PC generates an ARP reply that is unicast in nature.
2. Dynamic Host Configuration Protocol (DHCP):
The DHCP server assigns an IP address automatically to the host machine. In a small network, we can configure an IP address manually, but in a larger network, we can’t assign IP addresses individually to each machine.
So, we configure the DHCP server so that all hosts automatically receive an IP address.
To get an IP address, there are 4 DHCP messages that are exchanged between a DHCP server and a host.
Discover: First host sends a discover message to discover the DHCP server.
Offer: In response to the discovery message, the DHCP server sends an IP address.
Request: After getting the offer message, the host sends a request message to the DHCP server, I (host) am OK with this IP address. Please send full configuration details.
Acknowledge: In the acknowledge message, the DHCP server sends an IP address with all essential configuration.
All four messages are broadcast. This process of getting an IP address is also known as the DORA process.
3. Spanning Tree Protocol (STP):
Spanning tree protocol is used to reduce layer 2 loops. In general, to ensure network availability, some extra links are added. These extra links are also known as redundant links. They act as backup links, which means, if any active link fails, then traffic shifts to these backup links.
We saw, the purpose of adding these links is good, but these links have some cons also; these links also create loops at layer 2, and because of these loops, broadcast storm and MAC instability problems arise.
Now let’s see how STP reduces layer 2 loops. By default, STP is running in all manageable switches. By putting extra links in block mode, STP creates a single path between each point.

4. Secure Shell (SSH) and Telnet:
SSH and Telnet are used to remotely access the device. SSH is preferred over Telnet, as Telnet is less secure and sends data and passwords in plain text, so there is a possibility that anyone can view the passwords, while SSH sends encrypted data, and no one can view the actual data.
5. Hot Standby Routing Protocol (HSRP):
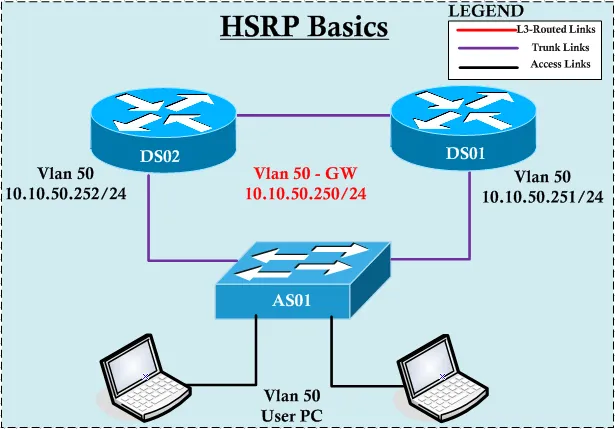
HSRP is also known as the gateway redundancy protocol. It is Cisco's proprietary protocol. HSRP is used for load balancing the traffic. In general, to ensure 24/7 network connectivity, enterprise networks have 2 internet connections from 2 different vendors so that if one goes down, traffic will shift to another, and this is achieved with the help of HSRP. In HSRP, there are 2 routers, one operates in active mode and another in standby mode. If, due to some technical issue active router goes down, then traffic will shift to the standby router.
6. Open Shortest Path First (OSPF):
OSPF is the interior gateway dynamic protocol. A dynamic protocol means it learns routes dynamically or whenever a change occurs in the topology, it automatically updates the routing table.
It works on the shortest path first algorithm to calculate the best path from available paths.
OSPF is a link-state protocol. To advertise routes to neighbours, OSPF uses Link State Advertisements (LSAs). AD value of OSPF is 110.1
TCP and UDP protocols:
TCP stands for Transmission Control Protocol. UDP stands for User Datagram Protocol.
Both are transport-layer protocols.
7. TCP Transmission Control Protocol:
TCP is a connection-oriented protocol; first, a connection is established between the sender and the receiver, and then the actual transmission starts. To establish a connection in TCP, there is a particular procedure that is known as the 3-way handshake process.
3-Way handshake image is inserted
The first sender sends a SYN message to the receiver.
In response to a syn message, the receiver sends a syn/ack message to the sender.
In response to a syn/ack message, the sender sends an ack message.
Here, syn stands for synchronize, and ack stands for acknowledge.
Transmission via TCP protocol in CCNA is reliable because there is an acknowledged message that conveys the status of packets (lost or received). It means if a packet is successfully received, it sends the message packet is received, and if a packet is lost, then it acknowledges the sender. A packet is lost in the middle. Please re-transmit the packet.

8. User Datagram Protocol (UDP):
UDP is a connectionless protocol. Also, there is no acknowledgement; if a packet is lost, it means it’s lost. It is not reliable. UDP is useful in VoIP applications. Note: Differences between UDP and TCP and 3the way handshake are the most commonly asked questions in the interview.
9. HyperText Transfer Protocol (HTTP):
HTTP is an application-layer protocol. HTTP is used to pull the content of web pages from the web browser.
10. IEEE 802.1Q
IEEE 802.1q is a VLAN tagging protocol. VLAN tagging is done to identify which VLAN the packet belongs to. Many times, IEEE 802.1q is known as dot1Q.
11. DTP Dynamic Trunking Protocol
DTP stands for dynamic trunking protocol. DTP allows Cisco switches to dynamically learn their interface status (access or trunk). It means when one switch interface is manually configured, another switch interface dynamically learns the status by looking at the manually configured interface status (no need to do manual configuration in both switches). It is Cisco's proprietary protocol. By default, DTP is enabled in all switches.
12. SNMP- Simple Network Management Protocol
SNMP stands for Simple Network Management Protocol. SNMP is used to monitor and manage the network devices (routers, switches, printers, etc.
The founder of Network Kings, is a renowned Network Engineer with over 12 years of experience at top IT companies like TCS, Aricent, Apple, and Juniper Networks. Starting his journey through a YouTube channel in 2013, he has inspired thousands of students worldwide to build successful careers in networking and IT. His passion for teaching and simplifying complex technologies makes him one of the most admired mentors in the industry.




