
Cisco CCNP
Enterprise / Security / Data Center
CCNP Enterprise is a professional-level certification designed especially for candidates thriving to excel in networking. After completing the CCNA certification training, one can enroll for the CCNP Enterprise certification. The CCNP Enterprise course can help you make up to 12+ LPA as a fresher. The CCNP Enterprise training is for those who really want to move ahead in the networking field and become Network Engineers.
Best
Curriculum
World's biggest
virtual labs
Learn Directly
from Engineers
Best
IT Infrastructure
Applications are Closing Soon, Register Now!
Apply Now for Next Class &
Get 5 Days FREE Fundamental Course
* Your information is secure with us
Curriculum designed to clear CCNP Exam
- Enterprise Network
Understand design principles used in an enterprise network. - WLAN deployment
You will understand the characteristics of network topology architectures. - Cisco SD-WAN solutions
Explain the working principles of the Cisco SD-WAN solution. - Wireless QoS
Describe concepts of wired and wireless QoS. -
Switching mechanisms
Differentiate hardware and software switching mechanisms.
- Virtualization technologies
Describe device virtualization technologies. - Path Virtualization technologies
Configure and verify the data path virtualization technologies. - Virtualization concepts
Describe network virtualization concepts.
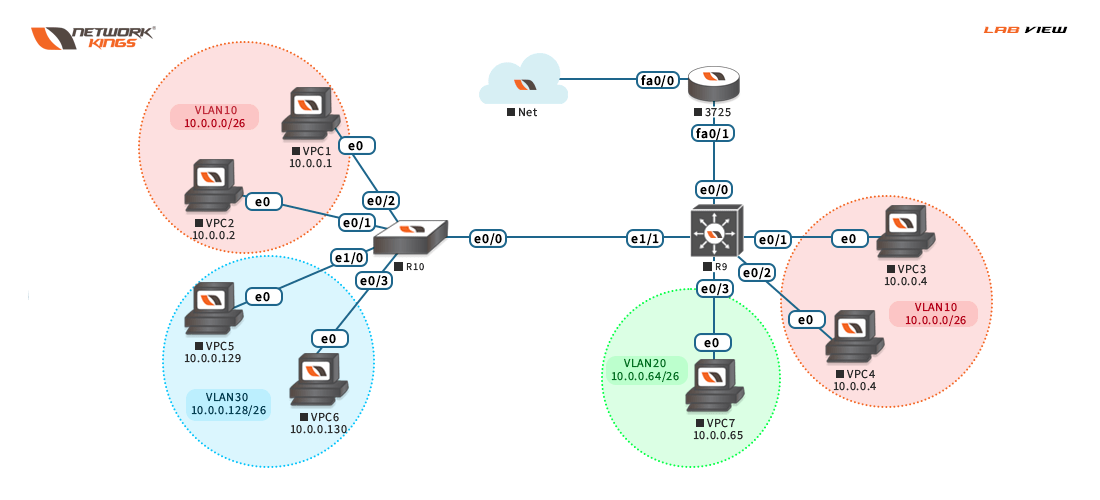
- Layer 2
Learn to troubleshoot and configure the following. - Layer 3
Learn routing concepts, configure, and verify OSPF environments and eBGP. - Wireless
Describe Layer 1 concepts, access point discovery, and join process. - IP Services
Describe, configure and verify related protocols.
- Network Assurance
Diagnose network problems using various tools.
- Debugs, conditional debugs
- Trace route
- Ping, SNMP, Syslog
- Configure and verify:
- SPAN
- RSPAN
- ERSPA
- Configure and verify device access control
Lines and password protection and Authentication and authorization using AAA - Configure and verify infrastructure security features
ACLs and CoPP - REST API security
- Configure and verify wireless security
EAP, WebAuth, and PSK - Components of network security design
Threat defence, Endpoint security, etc.
- Automation
- Python components & script
- Construct JSON-encoded files
- Data modelling language benefits
- APIs
- Interpret REST API response code
- Construct EEM applet
- Compare agent vs Agentless orchestration tools
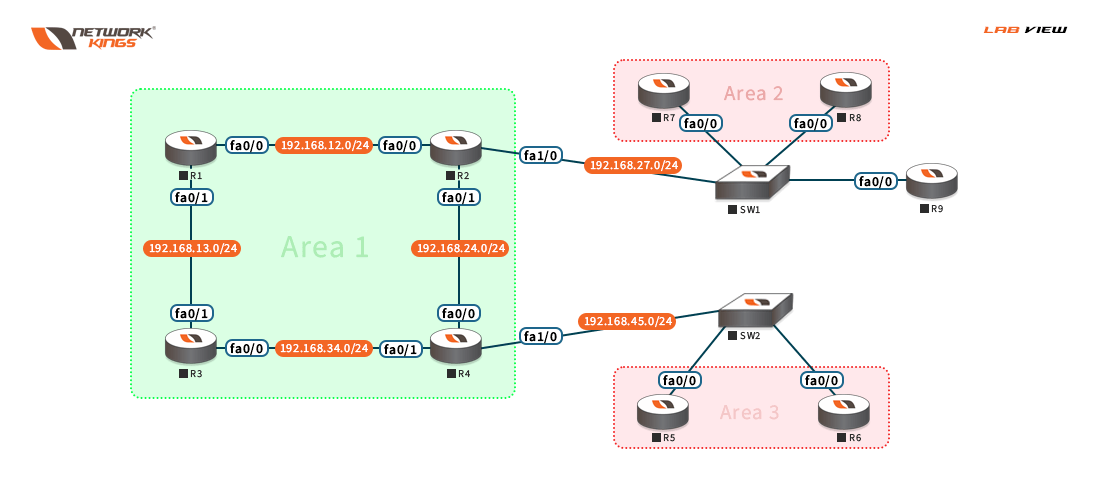
- Basic OSPF Configuration
OSPF Overview - OSPF LSAs
Router LSA, Network LSA, etc. - OSPF Multi-Area and Multi-Domain Functionalities
Configuring a Multi-Area-Multi-Domain Network - OSPF Area Types
Configuring a Stub Area, Configuring a Stubby Area, etc. - Redistribution in OSPF
Configuring the Multi-Domain Topology for Redistribution - OSPF AdvancedVirtual Link
- Basic eBGP Configuration
BGP Overview, Configuring Basic eBGP, etc. - iBGP Configuration
Configuring Routing Protocol for iBGP - Filtering and Summarization
Access-lists and Prefix-lists - BGP Attributes
BGP Attributes – Overview
- MPLS introduction
- MPLS Labels
- MPLS LDP
- VRF
- MPLS Layer 3 VPN
- MPLS Route Distinguisher and Route
- Targets
- MPLS with OSPF configuration
- Apply routing protocols – OSPFv2, OSPFv3, MP-BGP, PIM, FHRP
- Apply switching protocols such as RSTP+, LACP, and vPC
- Apply overlay protocols such as VXLAN, EVPN, and OTV
- Apply ACI concepts – Fabric setup, Access policies, VMM, Tenant policies
- Analyze packet flow (unicast, multicast, and broadcast)
- Analyze Cloud service and deployment models (NIST 800-145)
- Describe software updates and their impacts – Disruptive/nondisruptive, EPLD, and Patches
- Implement network configuration management
- Implement infrastructure monitoring such as NetFlow and SPAN
- Explain network assurance concepts such as streaming telemetry
- Implement Cisco Unified Compute System Rack Servers
- Implement Cisco Unified Compute System Blade Chassis – Initial setup, Infrastructure Management, Network Management, Storage Management, Server Management
- Explain HyperFlex Infrastructure Concepts and benefits (Edge and Hybrid Architecture vs all-flash)
- Describe firmware and software updates and their impacts on B-Series and C-Series servers
- Implement compute configuration management (Backup and restore)
- Implement infrastructure monitoring such as SPAN and Intersight
- Implement Fiber Channel
Switch fabric initialization
Port channels
FCID
CFS
Zoning
FCNS
Device alias
NPV and NPIV
VSAN
- Implement automation and scripting tools – EEM, Scheduler, Bash Shell and Guest Shell for NX-OS, REST API, JSON and XML encodings
- Evaluate automation and orchestration technologies – Ansible, Puppet, Python, POAP, DCNM, UCSD, PowerShell
- Apply network security
AAA and RBAC, ACI contracts and micro-segmentation, CoPP
AAA and RBAC, Keychain authentication
AAA and RBAC, Fabric binding
- ASA Overview and History
- ASA deployment
- Bootstrapping and basic ASA configuration
- ASA traffic flow & ASA routing
- NAT
- Modular Policy Framework (MPF)
- Transparent firewall
- QoS
- ASA HA & ASA clustering
- Security context
- Introduction and overview
- Firepower deployment
- Firepower traffic flow
- Access Control Policy
- Device and object management
- Network Discovery & Intrusion Policy
- NAP and pre-processors
- File detection and AMP4N
- SSL decryption & Identity policy
- Correlation policies & Event analysis
- Basics of cryptography
- Introduction to IPSec and PK
- VPN types and modes
- Site-to-Site VPNs
- GETVPN
- FlexVPN
- SSL VPN
- Clientless RA VPNs
- AnyConnect VPNs
- VPN load balancing and HA
- Layer 2 Threats and Mitigation
- Implementing network foundation protection framework (NFP)
- Understand and secure MP-CP
- Secure management traffic
- Secure Infra device images and config files
- Securing routing protocols
- WSA proxy services & Integrated L4TM
- User identity and authentication
- Web security policies
- URL filtering & SSL decryption
- Bandwidth control & AVC
- Outbound data security
- SMTP Overview & Relay
- ESA packet flow & Reputation filters
- AS and AV & Outbreak filters
- Content Filters & Content Security
- AAA framework overview
- RADIUS and TACACS+
- IEEE 802.1x
- ISE introduction and overview
- ISE and AD integration
- Wired and wireless 802.1x
- Guest access & ISE posturing
- Device profiling
- BYOD, MAB & TrustSec
- ISE in SDA deployment
- NetFlow and deployment scenarios
- Netflow in Cisco IOS and IOS-XE
- StealthWatch Management Console and Flow Collector
- CTA and ETA
- AMP4E introduction and overview
- Licensing
- AMP4E Console
- Managing policies
- Best practices
- Malicious investigations
- Introduction to Threat Grid
- Cloud vs On-prem
- TG File analysis
- CTR and SecureX
- Why and What of DNS?
- DNS Importance
- Umbrella introduction
- Umbrella use cases
3X your salary prospects with CCNP certification

CCNP by Mr. Sumit
Network Consultant

60+
hours of learning

1000+
Enrolled Students

Access to the world’s
biggest Cisco labs

Live interactive
classes
Our Students got job at







24x7 Lab Access
We offer world's biggest virtual labs
Our Alumni Placed at the Big IT firms...

Pradipta Sannyasi
Network Engineer

Pradipta Sannyasi
Network Engineer
- Phone:+1 (859) 254-6589
- Email:info@example.com


Kartick Mondal
System Engineer

Kartick Mondal
System Engineer
- Phone:+1 (859) 254-6589
- Email:info@example.com


Harsh Sonker
Associate Consultant

Harsh Sonker
Associate Consultant
- Phone:+1 (859) 254-6589
- Email:info@example.com


Ilyas Khan
Network Administration Trainee

Ilyas Khan
Network Administration Trainee
- Phone:+1 (859) 254-6589
- Email:info@example.com


Disclaimer- @2011-2023-Network Kings. All Rights Reserved.
We do not claim the ownership of the logos used above. They only belong to their respective organizations.
